The huge download button doesn’t give you the GPG signature of the apks, so you need to go to https://f-droid.org/repository/browse/?fdfilter=f-droid&fdid=org.fdroid.fdroid, as linked to in the wiki entry.
- Download the apk and the GPG signature for the latest version.
- Download the public key (I found it at pgp.mit.edu). Type:
gpg --keyserver pgp.mit.edu --recv-keys 0x41e7044e1dba2e89 - Verify the signature. Type:
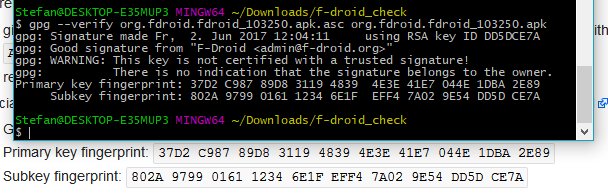
gpg --verify org.fdroid.fdroid_103250.apk.asc org.fdroid.fdroid_103250.apk - If you did everything correctly, the following output should appear. Check if the fingerprints match!