Ok I’ll test the dynDFE method.
I’ll report here my progress, so this post is to be updated ![]()
1) find the zip file
Found two links for dynDFE v2, here and here. checked the md5sum, both files are the same.
# Disable Force Encryption V2
# By reikaze
# Based on Zackptg5's DFE script
On another link I found four versions for vayu, not sure if those ones are device-specific…
prin " Disable Force Encryption V3"
prin " For Android 13"
prin " By Kamisato Rei"
prin " Mod by alanndz"
prin " Based on Zackptg5's DFE script"
2) backup my device
As you read above I did a full disk image with dd.
I want also to test two apps that I read about on this forum ![]()
Namely Neo Backup and Swift Backup. I’d like to compare them to my old Titanium Backup.
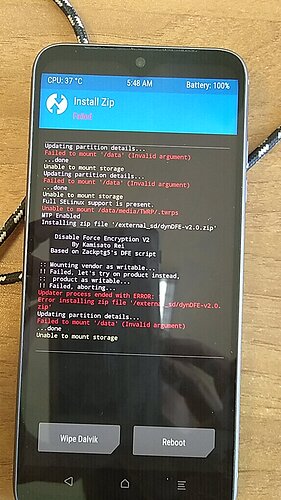
3) flash the zip file
That’s where the fun will start…
… or not, the script failed ![]() .
.
[Image taken with my FP2]
Do I have to wipe before? (I was guessing first flash the zip, then wipe, but I may be wrong)
Is a factory reset enough, or do we have to select manually (several?) partitions to wipe?