Do not find any info at lineage page which security items are included in lineage-14.1-20180123 for Fairphone 2.
The changelog is here: Fairphone 2 - FP2 - LineageOS 14.1 Changelog
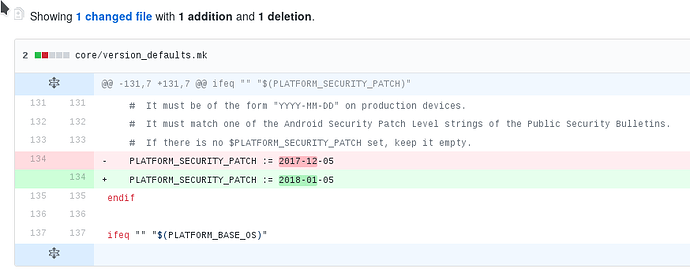
Amongst the changes for the 20180123 build is this: Bump security patch level to 2018-01-05 (links to the code review).
If you want to know what exactly the security patch level includes, you have to head over to Google’s Android Security Bulletin: Android Security Bulletin—January 2018 | Android Open Source Project
The thing is - and here I guess I have the same problem as phonefrog - if you look at the actual commit behind this “Bump security patch level to 2018-01-05” (https://github.com/LineageOS/android_build/commit/f05791524f2a57ae7473d1482a4e5fe9663cae58) it really only replaces that string.
And also all other entries in the changelog don’t look like they are related to security fixes.
For some outsider it might look like they just changed the label but not the content.
Thanks.
I found the following statement in the above Security Bulletin:
Note: CVE-2017-5715, CVE-2017-5753, and CVE-2017-5754, a set of vulnerabilities related to speculative execution in processors, have been publicly disclosed. Android is unaware of any successful reproduction of these vulnerabilities that would allow unauthorized information disclosure on any ARM-based Android device.
For me it is difficult to understand.
Does it mean that Android cannot reproduce the Spectre/Meltdown vulnerabilities? If so, we cannot expect any patch for this.
As I understand it, Android was patched against the vulnerabilities, and until now they think that nobody was able to successfully exploit those vulnerabilities in Android in the past … which of course is not a very solid statement regarding the past ![]() .
.
Well, there is also this statement: “See the Google security blog for more details.”
And there you get:
Android
Devices with the latest security update are protected.
Furthermore, we are unaware of any successful reproduction of this vulnerability that would allow unauthorized information disclosure on ARM-based Android devices.Supported Nexus and Pixel devices with the latest security update are protected.
Further information is available here.
And this further information is …
Android
On the Android platform, exploitation has been shown to be difficult and limited on the majority of Android devices.
The Android 2018-01-05 Security Patch Level (SPL) includes mitigations reducing access to high precision timers that limit attacks on all known variants on ARM processors. These changes were released to Android partners in December 2017.
Future Android security updates will include additional mitigations. These changes are part of upstream Linux.
Now did they really patch LineageOS or just replaced the date in the code as found by @Ingo ?
Good question, I’m not a developer, I can only google stuff ![]() … I found this here …
… I found this here …
https://cve.lineageos.org/android_kernel_fairphone_msm8974
… which looks pretty grim, but https://cve.lineageos.org/ at the same time states
Please note that the tracker needs to be manually updated by each device maintainer and it does not necessarily represent the real patch status of the kernel.
So you can’t go by that either.
@chrmhoffmann, can you help?
I just looked into it and this just sets a variable that gets used in the build-scripts.
I guess they pull this version of the AOSP as a basis. Therefore the hint that this data MUST match an android security patch level - otherwise the image won’t build.
But that is just an educated guess.
They just increase the strings, try if 14.1 still builds and then push the changes. They will do so until something breaks that workflow… ![]() so an “update” for them is just “change this string, run script, recieve patched image”
so an “update” for them is just “change this string, run script, recieve patched image” ![]()
Thanks for taking your time to actually look into this 
Here is some more insight: There are three main parts on your phone which contain security problems:
- Android itself (AOSP, Lineage OS etc)
- The kernel
- Firmware like the modem
Problems in category 1 get fixed by the linageos team and no extra effort is needed. That’s also why they bump up the patch level after fixing all security problems which were updated in AOSP and ported to lineageos. These are things like holes in media playback, the basic frameworks, the browser etc.
Unfortunately every device (or a group of devices) has its own kernel in lineageos. That’s the android_kernel_fairphone_msm89748 repository mentioned above. This means that the maintainers of a device need to fix security exploits in the kernel themselves. This service is not provided by the lineageos (core) team. Since there is only one security patch level displayed to the user and that is updated by the lineageos core team, it is possible that a lot of security fixes have not been applied to the kernel of a device.
That being said it actually looks pretty good for FP2. If you look at the commit history here, you can see that @chrmhoffmann does a good job of merging the latest releases from fairphone into the LineageOS Kernel for the FP2.
The third class of problems is in the firmware of the device. This includes the modem as well as wifi and other firmware. They are nearly always binary only and can only be updated by the chipset manufactures.
There is two places those firmware “blobs” can reside: The parts integrated into the ROM get updated by the maintainers (for FP2 see here)
For things like the modem which reside on their own storage partition, the end user is required to update those by hand. The official releases by Fairphone do this automatically, but it is not allowed to redistribute those files, so LineageOS can’t update them for you.
What I do is track the changes in FP Open OS, download every release they make and manually fastboot flash all the files except for recovery, system and data. A less error prone way is to follow the process described here: ✏ FP2 modem firmware
My conclusion? Don’t trust the security level shown in LineageOS. Each month there are a lot of security problems described in the Android security advisory. Some are in AOSP, some are in the kernel and some are in the firmware. All these get fixed eventually if you use the official Fairphone releases and they are very open about this. E.g. some of the bugs (in the firmware) can only be fixed by the hardware manufacturer and fairphone has to wait. That’s why they often don’t update the patch level to the current month, even though most bugs have been fixed. Just because they are missing a couple from their suppliers.
On LineageOS nobody cares if the kernel was updated or not. Same for the firmware. The security patch level gets updated for all devices. It only reflects the state of category 1 problems mentioned above.
What can you do? Update your LineageOS regularly and install the latest firmware/modem updates. This way you will have a more secure system than 99% of the android users out there.
Very good and understandable explanation! Many thanks.
Looking on XDA, I saw this app from Security Research Labs that apparently will indicate whether the patch level is correct and all the patches are in place.
https://play.google.com/store/apps/details?id=de.srlabs.snoopsnitch
I’m not rooted, so ran the test, 10 show as inconclusive which might be due to not being rooted and shows that 3 patches are missing: CVE-2017-0592, CVE-2016-6760 and CVE-2016-6761
That’s pretty good overall, and maybe this would make it easier for the cve checker here updated? https://cve.lineageos.org/android_kernel_fairphone_msm8974 @chrmhoffmann?
This topic was automatically closed 183 days after the last reply. New replies are no longer allowed.