I’ll ask FP support if they can patch all their phone models, including those that don’t have Qualcomm support anymore. Since this part seems open source, it is probably possible. But things like this underscore the importance of having chipset vendor support.
And while Apple has consistently patched and remediated security flaws in its proprietary version of ALAC, the open-sourced variant of the codec has not received a single update since it was uploaded to GitHub 11 years ago on October 27, 2011.
Apple and their relationship with Open Source, always a pleasure… ![]()
But Qualcomm and MediaTek building their audio decoders on this rotten foundation, that’s another level of irresponsibility, especially for the big players they are ![]()
The mentioned Qualcomm CVE-2021-30351 was fixed in the December 5 patchlevel update of Android. I believe all qualcomm-based fairphones have been brought to this patchlevel by now? My FP4 definitely is.
I’m mostly wondering for those models that don’t have Qualcomm support anymore.
FP2 and FP3 are as well…Overall I guess we need some confidence that Fairphone employees know their job and will do ther best to always apply security issues asap and that there should be no need to remind them about this
Do you have a source? Especially for the FP2.
My FP2 claims it’s at the 5 Feb 2022 patchlevel. It has to include a fix for that CVE (if it was vuln in the first place) to claim that. So let me be your source ![]()
what do you mean? I have a FP2 and FP3 as source that show me the security patch level is 5th Feb 22? Where is your source saying this patch was only applied to still supported QC SOCs? In the corresponding Quallcomm Bulletin e.g. the SD632 (FP3) SOC is not listed as affected, so are you saying this means the secutiry patch was not for this SOC or does this mean this SOC was not even affected?
Edit: neither can I find the SD801 listed in the QC security bulletin under affected chipsets
https://docs.qualcomm.com/product/publicresources/securitybulletin/december-2021-bulletin.html
German but quite clear in my eyes
Wer ein Android-Gerät besitzt, sollte sicherstellen, dass das Patch Level mindestens Dezember 2021 beträgt.
But that’s the point, right? It’s indeed in the Qualcomm section. If your phone doesn’t have Qualcomm support anymore there is no reason to believe you have that fix. This was also brought forward in the “sustainable software development” video I shared in this thread. When Qualcomm pulls out you’re left with a gap in security updates.
my understanding of the QC sec. bulletin and all other statements I read is different, I dont see any hint saying the QC patch was only applied to new and still QC supported chipsets/devices. So there is a very good reason in my eyes to believe both my devices received that patch if needed.
Affected in my eyes does not list the devices getting the fix, but listing the chipsets that were affected by this vulnerability (SD750G is listed). So I still dont understand why you think FP2 or FP3 or even FP4 would not have received this security patch as needed.
So maybe I’m too naive here, but I’m still missing a proof that FP2 and FP3 are potentielly not save due to this and I’m confident that FP is doing the needful.
Btw. its a closed source component as far as I can see in the corresponding Android security bulletin
From that webinar from FP and from what I heard from LineageOS developers I believe you don’t get those Qualcomm fixes if there is no involvement from Qualcomm. E.g. I asked the devs that maintain the Pixel 3, they said that you won’t get any Qualcomm specific fixes, so no Bluetooth/WiFi/modem fixes, etc. But I’ll relay this question to FP support, to make sure.
yes might be I dont understand well and why not explaining it better to me, when you know better? Sorry but you want me to proof, however I dont see your proof and I’m happy to learn and correct my view.
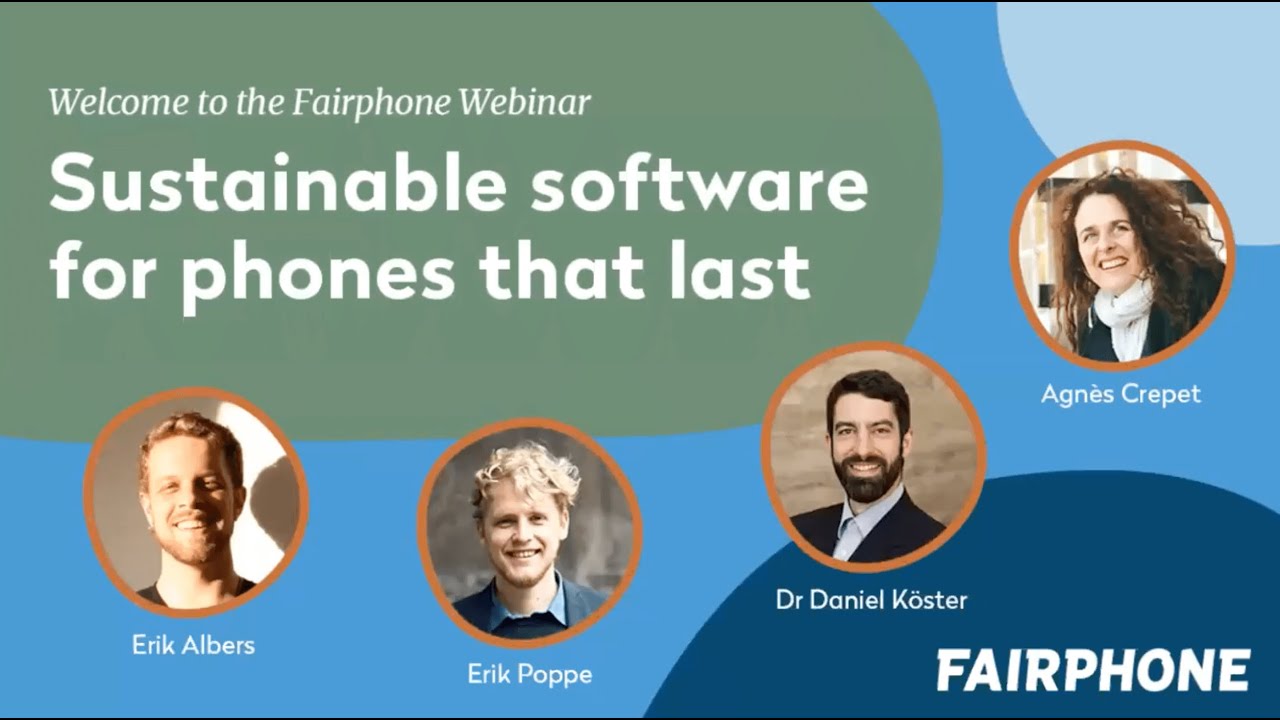
Anecdotes and guesses are not proof indeed. I’m trying to find the bit in the presentation below where they mention this. But it’s quite long. I’ll ask FP support, then we have an official answer. But they key part to understand is that Android doesn’t include chipset software, that’s Qualcomm’s job. If they pull out, you won’t get these fixes since they are device specific.
Found it ![]() And I’ll post the answer from FP support as soon as I have it. Chipset firmware is what we’re talking about here, that’s Qualcomm’s part. But who knows, maybe these Qualcomm bits are generic and work on any device. Would be nice of course.
And I’ll post the answer from FP support as soon as I have it. Chipset firmware is what we’re talking about here, that’s Qualcomm’s part. But who knows, maybe these Qualcomm bits are generic and work on any device. Would be nice of course.
Graphene devs seem to agree that FP would not be as secure as other fully supported phones:
Yes overall its known that there are obstacles when it comes to QC support end, thats not that new. I personally dont like the scare stories and headlines when it comes to such vulnerabllities and I’m wondering what your idea was when writing the first post and thats why I was quizing you yesterday a bit “aggressive”.
Informing with good facts instead of luring headlines and short articles not giving all information is what I would be looking for in such cases.
FP2 is not supported since years already, so there would have been most likely many security issues before the above mentioned.
I dont want to say there are no security issues, nevertheless I neither believe with QC support end all FP2 and FP3 have to be thrown away due to that.
I’m still confident that if there is a way to patch this to FP2 and FP3 Fairphone will do this.
fwiw this is the alac omx decoder component which has dsp and audioserver integration (? I didn’t look too much), and it is not publicly available.
It should be possible to take those ~5 blobs from a patched device and either directly or shim them into an older device.
But if you look at the 21 other security issues in the bulletin for that month you realize what a losing battle such as task is and to just accept that vendor blobs will be insecure mess.
FP2 and FP3 Fairphone will do this
They might not be allowed to given whatever contracts they have.
This makes for a more human read ![]()
I’m just using the title of The Hacker News, which is not know for click bait and fear articles. If you read carefully, it’s critical. And knowing how FP handles this will give me an informed understanding of the security state of my device when Qualcomm drops support, a device that has my whole personal and professional life on it.
The initial post is still valid, because we don’t know right? Is it good to know? Yes. Is everyone interested or concerned, maybe not. But that doesn’t change the impact of this security risk.