Of course you are right, all methods have flaws, i hope that there will be warnings and further documentation available.
I agree we should do our best to inform users about pros and cons, and we should also test the security of the fingerprint reader. (Some in the market, esp on budget and mid range phones, are very easy to circumvent.) If you feel like helping out with that, that’d be appreciated.
On Pixel, it’s hold power, select lock.
I think that fingerprint have a really lack of security: you leave your password everywhere you go, also on your smartphone is plenty of post-it with yours. But it nevermind because with a device rooted I can decide what kind of smartphone I want and which data I will share.
First step will be deactivate this module and block access to my data.
This and 3 posts below were moved here from iFixit's Fairphone 3 teardown is up – 10/10
Am I seeing this right? The fingerpring sensor can be removed? 
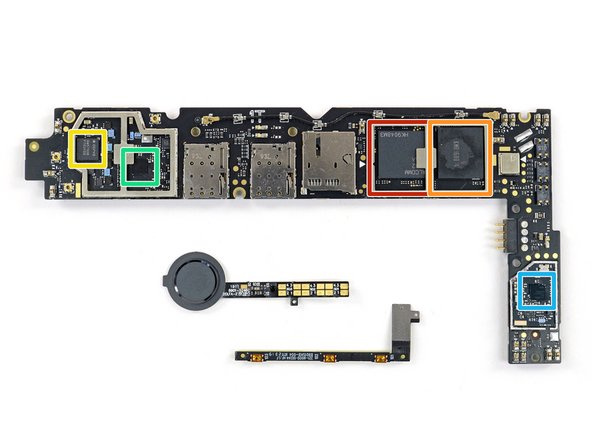
Yes, but then you’ll have an ugly hole on the back of your phone and your IP54 certification is gone.
I just saw that the fingerprint sensor is connected to the motherboard by spring contacts. So just tape the contacts on the PCB and you are fine and have an untouched looking FP3.
We just need the design files for the cover and 3D print them without the hole.
3D-printing though would use more plastic/resources than simply isolating the contacts.
And you keep the perfectly fitting cover. 
Giving away the unused fingerprint sensor to someone who might have a broken one (if they even break) would use less resources then them having to send in their FP3 to support to get their FP3 replaced and the old one sent back to the factory to be refurbished.
Also I’m sure I could find someone who’d take my original cover.
Sic!
But hey, I was just making fun. I am not dogmatic, when it comes to such decisions. ![]()
The fingerprint reader doesn’t seem to me to be the real problem. The important question is wether the biometric data are stored locally or in a remote cloud - and this may vary according to the app using fingerprints.
That’s on top.
I guess, as @Akiro already pointed out, the problem, to start with, is the fact, that a fingerprint reader can be “fooled”, as you leave your fingerprints everywhere, especially all over the phone itself.
I have seen a documentary, where a fingerprint was used to get access via such a device. It took just some kind of tape (if I recall it correct).
Here’s an article with links to various methods to pass such a device:
And here an article on biometrics security (including fingerprints) in general:
Finally, here are some “How tos” on fingerprint faking:
The future:
We found a breach in our security system. Please change your fingerprint to keep your account safe.
Your new fingerprint has to contain at least 100 long and 100 short epidermal ridges, 3 knife-scars, 2 burn-scars & 1 blister and it may not be similar to your former fingerprint.
You wish. The future is now …
Hm, how come I am not surprised to read about this…
The leaks above are a real risk. However, apps on phones using the standard Android Fingerprint implementation (probably all) do not have access to the fingerprint fingerprint at all, let alone the raw data to upload. The fingerprint is generally stored on devices only. This is why you have to unlock your phone with a pin even when using a fingerprint after reboot: The fingerprint is stored on an encrypted enclave on device that can only be accessed with you PIN. In theory, of course, someone having access to the devices software could manipulate the firmware and os, but normal apps from the Play Store can not.
So how can apps display a Fingerprint dialog? See the Android Developer docs for details:
https://developer.android.com/reference/android/hardware/biometrics/BiometricPrompt
In short, the requests a dialogue and fingerprint verification from the OS (Android) and gets a response if the fingerprint was matched.
What matters is the false positive amount. How high is the chance that a random person can unlock your smartphone via fingerprint because reasons (similar fingerprint, a bug in the software, etc).
Not every implementation is as strong as the other. Especially of cheaper Android devices. We don’t know how good Fairphone’s is.
If you’ve been a naughty boy I recommend to put your device off at night so police in morning can’t simply enforce you to unlock your device with your finger.
You can’t be enforced to unlock your smartphone via PIN, but you can be forced via fingerprint.
Sometimes PIN is weaker than fingerprint. For example, people around you may see how you enter your PIN. I’ve done this as a game whilst travelling, and found it rather easy. Pattern is even easier. If I was a cop and I were after you, I’d just follow you until I see you entering your PIN. Then I grab you. Very easy.
As for physically removing the fingerprint. Just not using it should be good enough. If you’re unable to trust the software to not use the fingerprint reader, then you have a whole lot of different things to worry about as well.
This topic was automatically closed 182 days after the last reply. New replies are no longer allowed.